The

Blog
Vulnerability Advisory: Unauthenticated Remote Code Execution in ScadaBR 1.2.0 Executive Summary The DREAM Security Research Team has identified four security vulnerabilities in ScadaBR 1.2.0, an open-source SCADA platform. These findings were reported to CISA and published on May 19, 2026. Successful exploitation of these vulnerabilities could allow an attacker to
Our Latest Black Hat Asia Talk: Introducing the RFC Analyzer Our Latest Black Hat Asia Talk: Introducing the RFC Analyzer Arad Inbar, a security researcher from our research group at DREAM, recently presented at Black Hat Singapore. The talk focused on using protocol specifications, specifically RFCs, as a primary surface
How We Discovered The Microsoft’s Plan For Mitigating Local NTLM Relay One of the most powerful ways to understand what a security patch actually fixes is to reverse engineer the binaries before and after the update. Vendors rarely disclose full vulnerability details immediately, but the code always tells the truth.
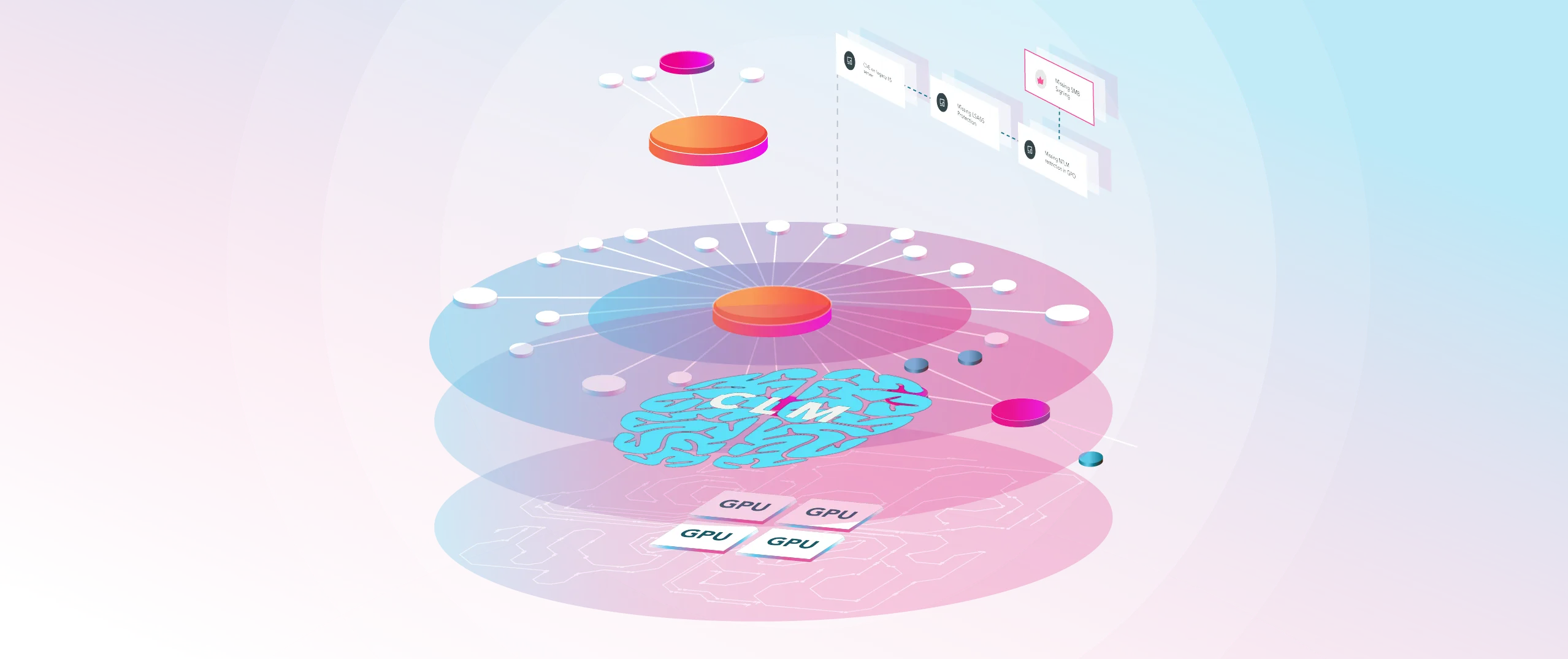
Six Lessons From Making Our AI Security Agent Explainable We built an AI agent for security teams. It analyzes configs, hunts for vulnerabilities, investigates threats. Here’s what we underestimated: security people are paid to be paranoid. They don’t trust systems they can’t audit. And honestly? They shouldn’t. So we built
Port 23, 30 Years Later: A Pre-Auth LINEMODE Bug in GNU Telnetd (CVE-2026-32746) A bug rooted in Telnet’s early-1990s LINEMODE logic survived into modern GNU Inetutils telnetd, leaving a pre-auth memory corruption path reachable before /bin/login, before passwords, and before PAM. Summary CVE-2026-32746 is a pre-auth out-of-bounds write in GNU
Vulnerability advisory: Pre-Auth Remote Code Execution via Buffer Overflow in telnetd LINEMODE SLC Handler This advisory is published in the public interest to enable defenders to assess exposure and apply mitigations. Responsible disclosure practices apply. Advisory ID: VULN-TELNETD-SLC-2025 Date: 2026-03-13 CVE ID: CVE-2026-32746 Severity: Critical CVSS 3.1 Score: 9.8 (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H)
When a Missile Alert App Becomes an Intelligence Tool In the middle of a war, trust is maybe the most fragile asset. Missile alert apps are not just software for civilians in Israel and in War Zones. They are lifelines. People rely on them for seconds that can save lives.
Hey Claude, Security is not just Code! Claude Code Security versus Dream Security Anthropic’s Claude Code Security announcement triggered predictable reactions across the industry. Excitement, curiosity, and in some corners, anxiety. Whenever a frontier LLM vendor steps into anything labeled “security,” the same question surfaces: is this the beginning of